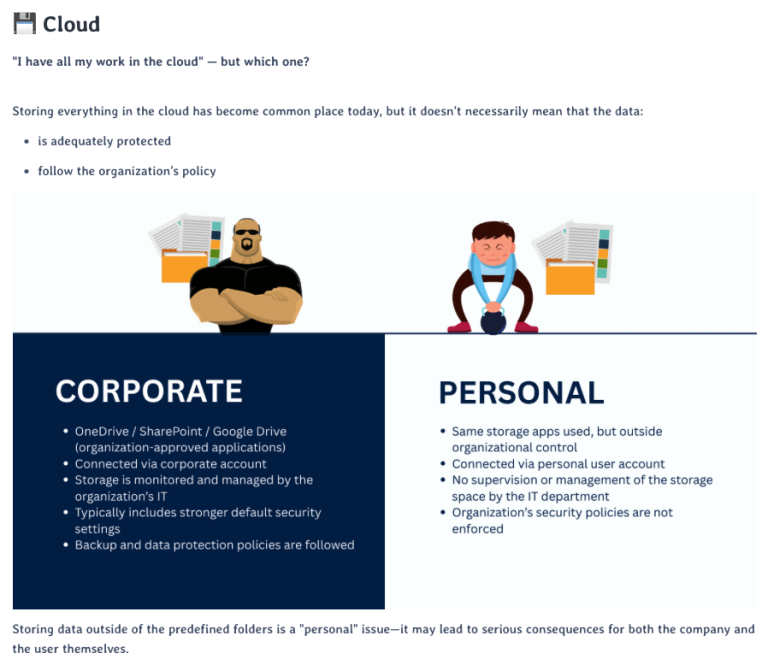
Organizations invest in modern security systems, yet a large percentage of attacks still succeed due to human error.
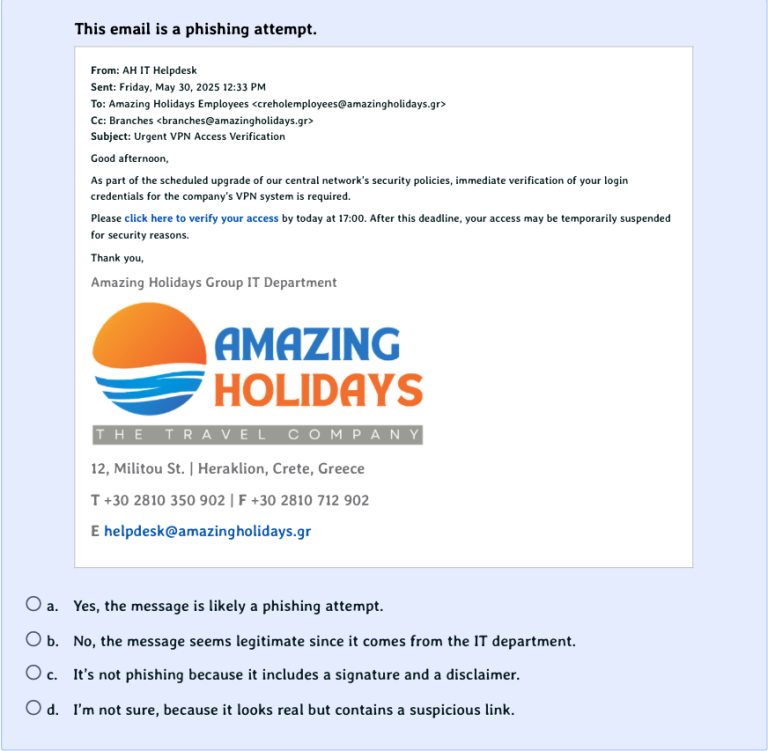
Phishing emails, deceptive messages, and social engineering techniques bypass technical controls and directly target user behavior.
Without proper training and continuous awareness, employees remain the most vulnerable part of the security chain — even in well-protected environments.